Yes, I can paste the code here, but how can it help you to debug? I think ZIP would be more useful, though for me the installation my own of extensions from ZIPs does not work for some unknown reason…
var test_instances = []
function startTest(url, test_index) {
var req = new XMLHttpRequest()
req.open("GET", url, true)
req.responseType = "document"
req.onload = function() {
processResponse(req.response, url)
test_instances.push({ index: test_index, url: url, pos: 0, result: null, ac: 0, cc: 0, pc: 0, xhrc: 0, errors: 0, paused: false })
document.getElementById('ifr').test = test_instances[test_instances.length-1]
var test = tests[entries[test_index].test_id].data
runOperation(test, 0, test_instances.length-1)
}
req.send(null)
}
function sendRequest(url, method, data) {
var ti = document.getElementById('ifr').test
var test = tests[ti.index]
var test_index = ti.index
var pos = ti.pos
var method = method.toUpperCase()
if (!url.match(/^http/)) {
url = url.length ? ti.url.split('/').slice(0, -1).join('/') + '/' + url : ti.url
}
if (!data) data = null
var req = new XMLHttpRequest()
req.open(method, url, true)
req.responseType = "document"
if (method == "POST") {
req.setRequestHeader('Content-Type', 'application/x-www-form-urlencoded')
}
req.onload = function() {
processResponse(req.response, url)
if (pos < tests[test_index].data.length-1) {
ti.paused = false
runOperation( tests[test_index].data, pos+1, test_index)
}
}
req.send(data)
}
function processResponse(response, url) {
result = response && response.children[0]
var ifr = document.getElementById('ifr')
while (ifr.contentDocument.children.length) {
ifr.contentDocument.removeChild(ifr.contentDocument.children[0])
}
var uri = new URL(url)
result.innerHTML = result.innerHTML.replace(/(href|src)="\//g, '$1="' + uri.origin + '/')
.replace(/(href|src|action)="(?!http:|https:|android-app:)([a-z0-9_-]+)/g, '$1="' + uri.origin + uri.pathname + '/$2')
.replace(/(fetch\(["'])\//g, '$1' + uri.origin + '/')
.replace(/(fetch\(["'])(?!http:|https:|android-app:)([a-z0-9_-]+)/g, '$1' + uri.origin + uri.pathname + '/$2')
.replace(/(\.open\(['"](?:GET|POST)['"],\s*['"])\//g, '$1' + uri.origin + '/')
.replace(/(\.open\(['"](?:GET|POST)['"],\s*['"])(?!http:|https:|android-app:)([a-z0-9_-]+)/g, '$1' + uri.origin + uri.pathname + '/$2')
.replace(/url\(([^("]+)\)/g, 'url("$1")')
.replace(/(href|src)=([^" \t]+)(\s+)/g, '$1="$2"$3')
.replace(/(url\("?)\//g, '$1' + uri.origin + '/')
.replace(/(url\("?)(?!http:|https:|data:)([a-z0-9_-]+)/g, '$1' + uri.origin + uri.pathname + '/$2')
ifr.contentDocument.appendChild(result)
ifr.contentWindow.eval("window.alerts = []; window.confirms = []; window.promts = []; window.xhr = []; " +
"window.store = {}; var prevent_xhr = false; " +
"var confirm_answer = true; var promt_answer = 'lightning'\n" +
"window.alert = function(msg) { console.log(msg); this.alerts.push(msg) }\n" +
"window.confirm = function(msg) { this.confirms.push(msg); return this.confirm_answer }\n" +
"window.promt = function(msg) { this.promts.push(msg); return this.promt_answer }\n" +
"if (!window.XMLHttpRequest.prototype._open) { window.XMLHttpRequest.prototype._open = window.XMLHttpRequest.prototype.open; window.XMLHttpRequest.prototype.open = function(method, url, async) { window.xhr.push({ method: method, url: url, data: null }); if (!window.prevent_xhr) this._open(method, url, async); }}\n" +
"if (!window.XMLHttpRequest.prototype._send) { window.XMLHttpRequest.prototype._send = window.XMLHttpRequest.prototype.send; window.XMLHttpRequest.prototype.send = function(data) { window.xhr[window.xhr.length-1].data = data; if (!window.prevent_xhr) this._send(data); }}\n" +
"window.parent = null; window.locationUrl = '" + url + "'\n" +
"if (!window._fetch) { window._fetch = window.fetch; window.fetch = function(url, options) { window.xhr.push({ method: 'GET', url: url, data: null }); if (options.method) window.xhr[window.xhr.length-1].method = options.method; if (options.body) window.xhr[window.xhr.length-1].data = options.body; if (!window.prevent_xhr) return window._fetch(url, options); }}\n" +
"window.parent = null; window.locationUrl = '" + url + "'")
var s = result.getElementsByTagName('script')
for (var i = 0; i < s.length; i++) {
try { ifr.contentWindow.eval(s[i].innerText) } catch(ex) { console.error(ex) }
}
fireEvent(ifr.contentWindow, 'DOMContentLoaded')
fireEvent(ifr.contentWindow, 'load')
if (ifr.test) ifr.test.paused = false
}
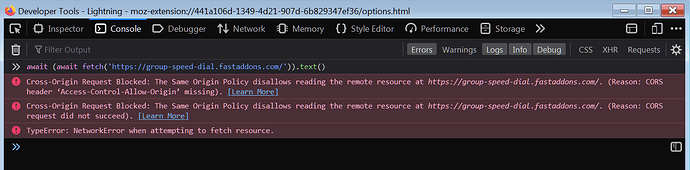
What really fails here is this:
var req = new XMLHttpRequest()
req.open(method, url, true)
req.responseType = "document"
if (method == "POST") {
req.setRequestHeader('Content-Type', 'application/x-www-form-urlencoded')
}
req.onload = function() {
processResponse(req.response, url)
if (pos < tests[test_index].data.length-1) {
ti.paused = false
runOperation(tests[test_index].data, pos+1, test_index)
}
}
req.send(data)